SOLUTIONS FROM
YOUR SIDE
OF THE TABLE


About Applied Technology Group (ATG)
Mission-Driven Cybersecurity, Rooted in the Deep South
Since 2016, ATG has been mission-driven to help organizations implement cybersecurity solutions with the least impact on usability and budget. That mission is led by seasoned experts with decades of experience in cybersecurity and critical infrastructure.
Leadership You Can Trust, Backed by Decades of Experience
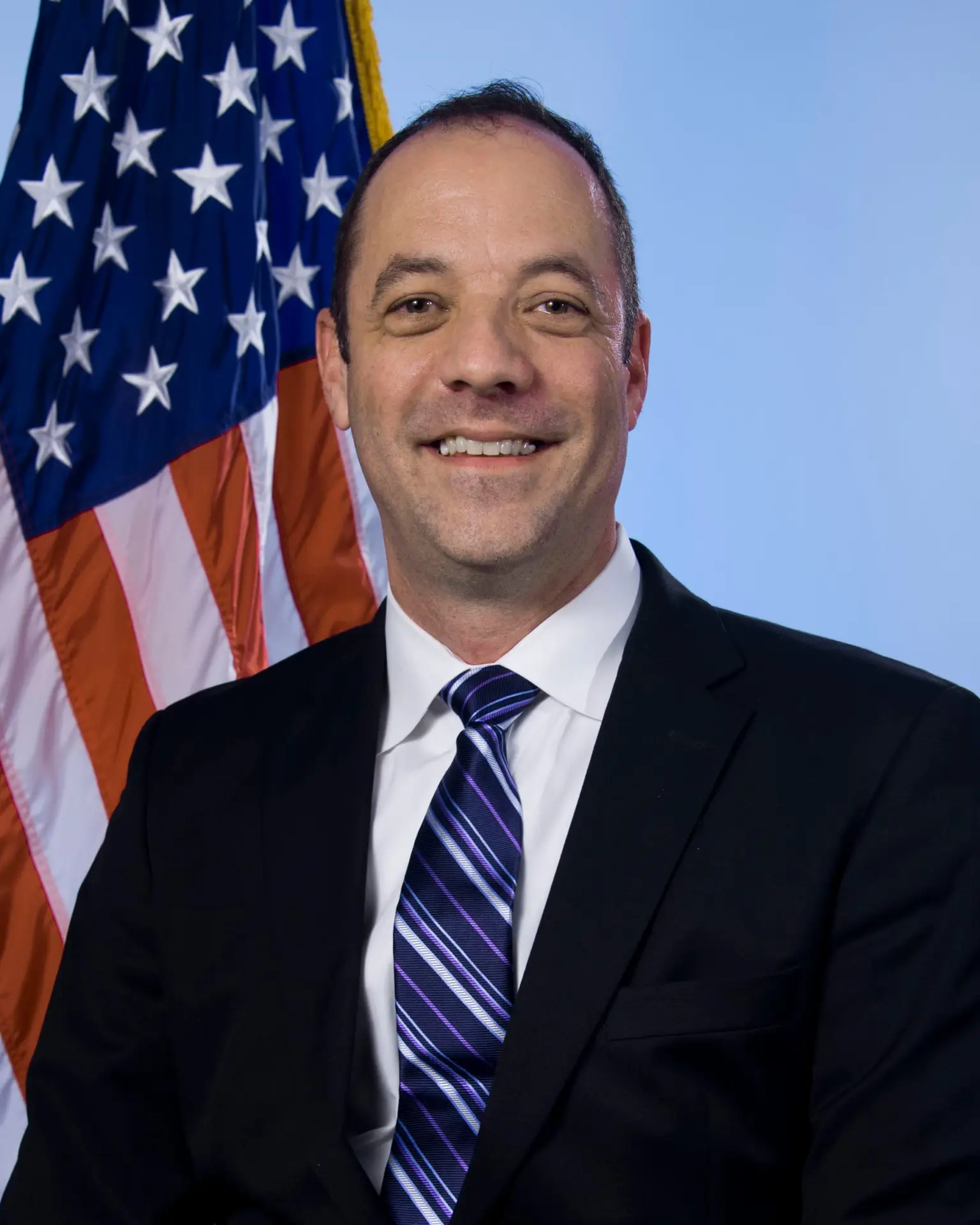
Shane Adams, CISSP, ISSAP, CISM
Principal
Our Leadership
Meet the Principal Behind ATG
For nearly two decades, Shane Adams has been a strategist and tactician in IT infrastructure and cybersecurity. He has led solutions ranging from single-user deployments to enterprise-scale systems supporting thousands of employees. His mission has always been the same: deliver secure, resilient, and scalable systems that meet business needs while following best practices.
Over the years, Shane has built systems in the toughest conditions — supporting recovery operations from a campground, performing implementations from a chemo chair, and even fielding questions from the FBI. These diverse experiences forged a unique perspective: security must be practical, adaptable, and aligned with the realities organizations face.
Certified as a CISSP, ISSAP, and CISM, Shane applies proven principles like the CIS Top 20 Critical Controls to help organizations move beyond “checklist” compliance and achieve true cyber resilience.
ATG's seasoned experts deliver executive-level guidance to help organizations make informed, strategic cybersecurity decisions. Our consulting services provide the critical insight your leadership team needs while ensuring seamless collaboration with operational staff to achieve mission success.
Cybersecurity programs can have many different requirements based on regulations, the attack surface, and the organization's risk appetite. ATG's unique expertise ensures that the correct framework and testing methodologies are always chosen. Our clients gain an insight into their security posture based on relevant standards and frameworks.
Security programs require constant attention to detail. Our experience shows that IT teams and network administration staff are often tasked with managing security tools. This works well until the organization calls on those teams to perform the functions they were intended to handle, such as handling outages, upgrades, and business growth initiatives. Our SOC team manages daily, weekly, monthly, and quarterly checklists for customers. These recurring processes are monitored by trained staff, who send alerts to your team. In many cases, our team also assists with remediation, so your team can focus on the business.
Our Services,
Guided by Core Values
Practical, proven solutions built on decades of cybersecurity experience.
